Digital Forensics Analysis
End-to-end digital forensics investigation simulating a real-world incident: analyzing phishing and business email compromise attack vectors, recovering deleted evidence from system images, and reverse engineering malware to reconstruct attack chains and identify threat actor TTPs.
[SCROLL TO EXPLORE]
View ProjectThe Problem
When an incident happens, the evidence doesn't wait for you. Files get deleted, logs get overwritten, and attackers obfuscate their tracks. A forensic investigator's job is to reconstruct what happened from whatever survives (email headers, memory artifacts, fragmented file systems, compiled binaries, et cetera) that weren't meant to be read. This project simulated exactly that scenario: starting with 8 compromised system images and working backwards to surface the full attack chain.
What's Included
- Phishing and BEC attack vector investigation including email header, attachment, and link analysis
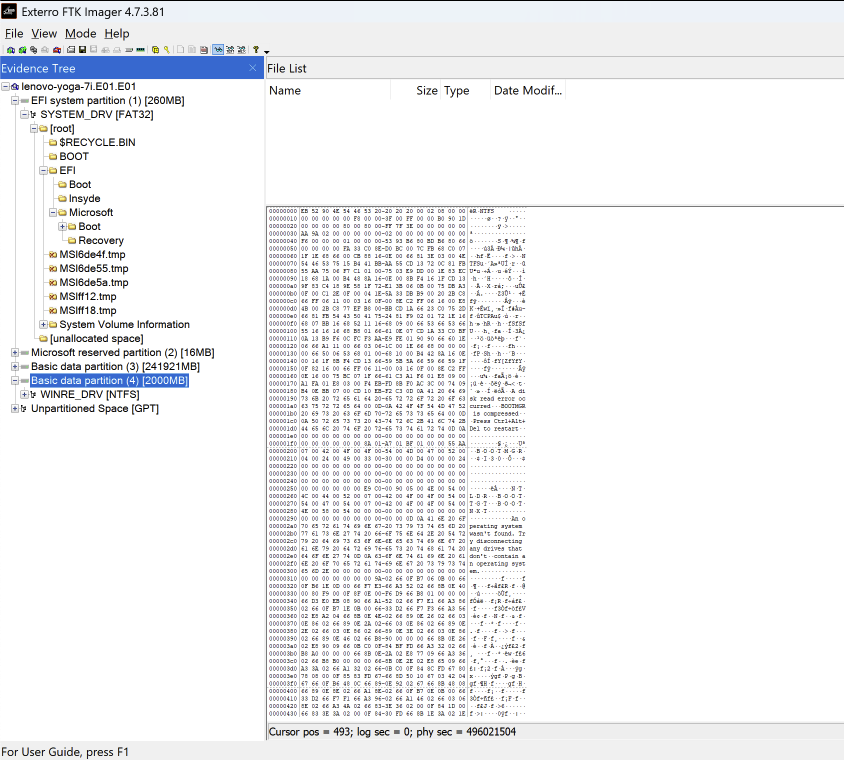
- Recovery of deleted and obfuscated evidence across 8 system images including hashes, user accounts, logs, documents, and metadata
- Reverse engineering of 20+ malware samples to identify threat actor TTPs and email-based attack chains
- Threat intelligence correlation across reassembled evidence to identify attack patterns
- Identification of 80+ functions, libraries, and security vulnerabilities through unknown executable analysis
- Forensic image and file system creation and inspection using Procmon and PeStudio
Impact
Reassembling a fragmented attack chain across 8 system images — recovering deleted files, correlating metadata, and reverse engineering the malware that started it all — mirrors exactly what incident responders face after a real breach. The ability to identify 80+ functions and libraries in unknown executables, and map them back to attacker behavior, is the difference between knowing an incident happened and understanding how, why, and what to do next.
Technical Stack
- Scalpel: file carving and deleted evidence recovery from system images
- FTK Imager: forensic image acquisition and file system inspection
- Ghidra: reverse engineering and binary analysis of unknown executables
- Binary Ninja: malware disassembly and TTP identification
- Autopsy: digital forensics platform for evidence analysis and correlation
- Procmon: process monitoring and forensic image inspection
- PeStudio: static malware analysis and executable inspection
- MITRE ATT&CK: TTP mapping and threat actor behavior classification